So, "GCSB assistance" is basically "NSA assistance", so when the Police asks for GCSB help, it's actually getting NSA help.
I buried the shit out of that lead last time. The only reason it didn't die there was that Juha Saarinen picked up the significance of the GCSB-NSA link and wrote about it. From there, the news made it on to Ars Technica, which got Slashdotted/Reddited/tweeted by Greenwald, which made me realise that, perhaps, this was news after all.
And that, perhaps, I shouldn't have put it in a throwaway line. Half way down a post about PGP keys. Made at 5pm. On the day Shearer resigned. After the GCSB bill passed.
Basically: I am the worst at newsing. Soz.
Partly, I figured that people already knew: David Fisher, on the back of the same documents, implied the same things two months ago. And partly, being the pessimistic apocalyptist that I am, I was already on "Depression", and forgot that everyone else was still on "Anger".
It also highlights how these stories (PRISM, GCSB etc.) work. Not only are they inherently complex and difficult to understand, but because there's so much of it coming out in so many pieces, it's really hard to know what "everyone knows". The fact that something is in the public domain, or even has been reported, doesn't mean that it's a part of the public discourse.
Now, we return you to your homework.
Part Two: Signing/Verifying Keys
This is part of a multi-part series on security, aimed at journalists but useful for anyone. They are intended to get you comfortable with the tools and help you understand the principles being them. These are short, easy learning exercises - *DO NOT use them to store or transmit sensitive information yet*. They are only effective one you understand all the layers and can put them together.
Let's say I send you an email, encrypted using your public key. I know who you are, because only you can decrypt that message. But how do you know who I am?
The magic of public-private keys is that they work both ways. When we encrypt messages, we use a public key to encrypt it, then a private key to decrypt it. "Signing" a message is doing the reverse. You're creating an encrypted signature using your private key, which can then be decrypted using the public key. This way, anyone can use your public key to verify that it was sent by someone with your private key (which is hopefully you).
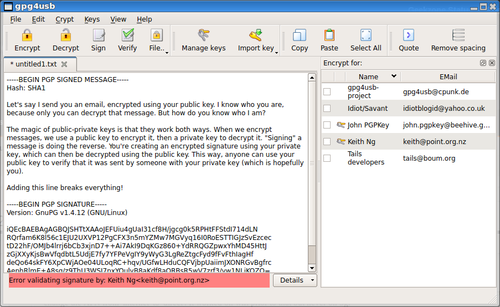
This message was signed with my key, so you'll need to have my public key to verify it (if you don't know how, go back and read part 1). To verify the message, copy and paste the whole thing into gpg4usb, then click Verify. The green message should pop appear down the bottom.
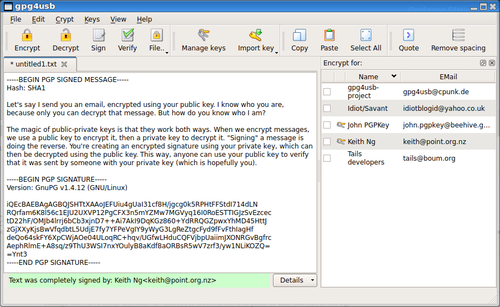
Every signature is unique because it's generated using the private key AND the message itself. If you change the message - even a single character - then the signature will be invalid. Try it!
You can sign your own messages by writing it normally, then selecting your private key and clicking the "Sign" button. Do this last, because making any changes to the message will break the signature. After this, you can encrypt your message like you would normally - the signature will get encrypted as well.
Now you know how to sign messages to prove that you were the one who wrote it - and not some hacker who's gotten into your email.
Next chapter: Publishing keys.