Welcome to your sudden but inevitable future of ubiquitous surveillance.
To an extent, I appreciate the arguments made by supporters of the GCSB Bill - it's not really a huge encroachment of mass surveillance powers, it is, mostly, just the formalisation of mass surveillance powers that have been encroaching for a decade. We are not fucked off because of the bill itself, really, but because we've finally been forced to pay attention to the barftastic overreach of state surveillance that's been happening around us.
At least, that's true for me. Thanks to the GCSB Bill, I finally got around to reading the Kim Dotcom affidavits. It's the best example we have of how "GCSB assistance" is actually rendered. The Police asked the GCSB for help in a one-page request (page 13 of this):
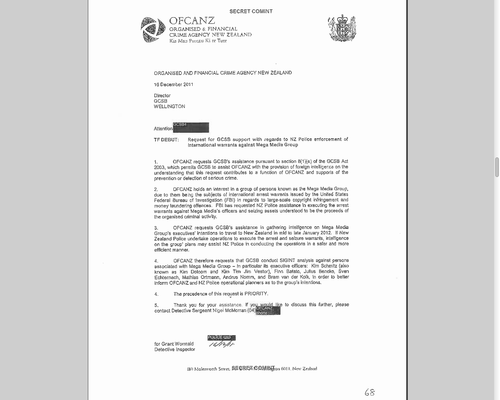
Once the GCSB's lawyer had a look at it, the Police provided a list of "selectors" to the GCSB (we now know from the PRISM documents that "selectors" is the term used to describe the search terms used to make PRISM requests):
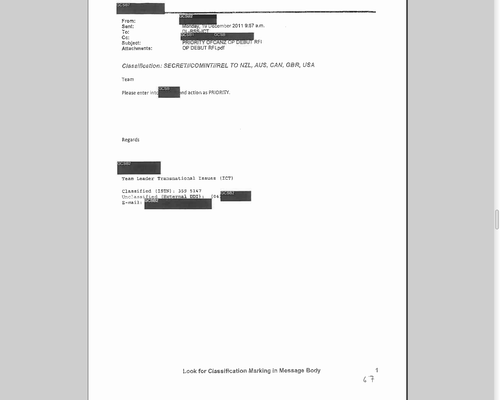
The selectors were entered into █████, in an email classified as "SECRET//COMINT//REL TO NZL, AUS, CAN, GBR, USA". In other words, the selectors were entered into a secret communications intelligence system, and this secret system was considered related to Five Eyes:
The email from the GCSB then described "traffic volume from these selectors": i.e. This secret system was capturing live traffic.
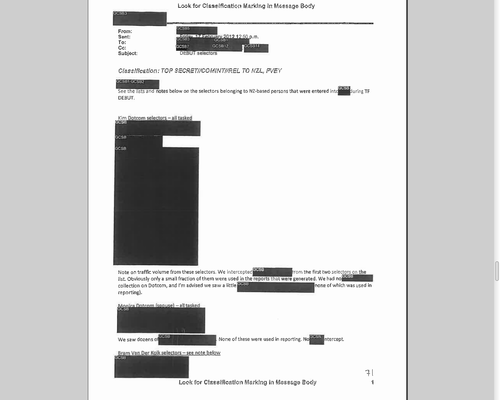
This is consistent with everything that we know about PRISM. Key has refused to comment on this.
What does this mean? It means that GCSB assistance is NSA assistance. It means that government agencies can tap into these powers as part of bread-and-butter law enforcement. Through the Bradley Ambrose case, we've seen that the Police are willing to use the full extent of their powers for entirely bullshit cases. Combine the two, and it makes me very, very queasy.
I ended my post in May with "we need to start by getting really, really fucked off". What is step two? Fortunately, there is a 25-year-old answer to this question: Encrypt everything.
Over the next however long it's going to take me, I'm going to be doing short posts on how to secretfy your stuff. Today's post is on encrypting text using public-key encryption.
Public-key Encryption (the uber-short version)
This technique is based on a pair of matching keys - one public, one private. Anything encrypted with one can only be decrypted with the other. Why? MATHS, that's why. The public key is then made public (my key is here), and anyone can use that key to encrypt a messsage. Only you - with the private key that you keep secret - can decrypt that message.
It's actually not that hard. The simplest tool for dealing with PGP keys is gpg4usb. Go download it and have a play. Purely for testing purposes, here is the public AND private keys for "John PGPKey" (right click on the link --> "Save link as.." to save the file). Open up gpg4usb and use the menu bar: Keys --> Import Key from.. --> File.
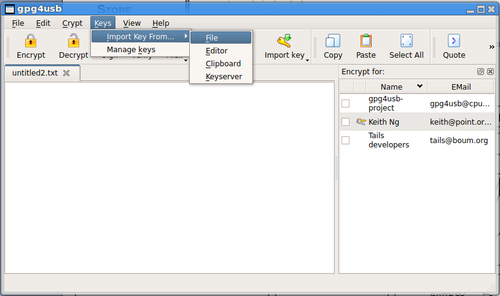
Select the .asc file you just downloaded. You can now use John PGPKey's private and public keys.
(Just to reiterate, this is for testing purposes only - you should NEVER put your real private key on the internet.)
Here is a message that's been encrypted using John PGPKey's public key. Open it up and copy and paste the garbled text into gpg4usb (including the BEGIN PGP MESSAGE and END PGP MESSAGE lines). Click on the "Decrypt" button. It'll ask you for a passphrase, which is "spicy panopticon in a dunnenad sauce" (this is a more reliable guide to making secure passphrases than your IT department).
(And no, you should not be putting the passphrases for your real private key on the internet, either. NOTE: Apologies if this didn't work before, I posted the wrong version of the key I was faffing around with.)
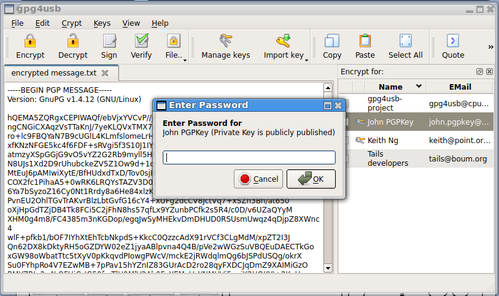
Enter the passphrase and BAM - you've decrypted a message! (If you haven't, check that you've copied the whole message, and check that you typed in the password properly.)
Now, to encrypt a message, just type things into the text box, select the key you want to encrypt with, and click on the "Encrypt" button. Pretty goddamn easy.
To create your own key, open up Keys --> Manage Keys. From the Key Management window, open up Key --> Generate Key. Fill out the boxes and go. You can export the public key and put it somewhere public - but let's not actually do that yet, until we have a way of securing your private key.
In the next part, we'll talk about publishing keys, verifying keys, signing with keys.