On 2 October 2014, the Police raided Nicky Hager's home as part of Operation Oracle - the hunt for Rawshark. During the search, Detective Jason Abbot found a piece of paper and passed it to Detective Joseph Teo. "We considered [the document] was of interest to the investigation because of information we had already obtained", Teo said in his affidavit.
That piece of paper was seized and designated NH025.
--
I first got in touch with Ben Rachinger in February this year, when he first started dropping docs publicly, but I didn't meet him in person until May, several weeks before his story aired on The Nation.
Contrary to the conspiracy theorists, Ben's story wasn't ignored by the MSM. There was a pretty mad dash initially to get his story, but it all happened under the radar as journos tried to scoop each other.
At least that's why it was under the radar at first. As Ben's story unfurled, it became increasingly fantastic: He was whistleblower, and hacker, and undercover agent for the Police, with sources at the highest level of government. Those who chased the story were wary as hell, and Ben had a tendency of turning on journalists who questioned his story, lumping them into a media conspiracy against him.
But for all the reasons not to believe Ben, he had hard evidence to back him up: Screenshots of messages and emails between him and Slater. And when The Nation ran their story, they did it after confirming that Ben really did have a relationship with the Police. His evidence could not be the work of a garden variety fantasist. This was either a truly spectacular hoax, with elaborate planning, screeds of details, and willing participation by Slater... or it was true.
Several days after our meeting, he gave me an encrypted file purporting to be the full chat logs between him and Cameron Slater, but it took another two months before he provided me with the password.
I still don't understand why he did this. But he did, and here we are.
--
NH025
Not long after Dirty Politics, rumours began circulating around the identity of Rawshark: That it was Rangi Kemara, a computer security researcher and one of the Urewera Four. With his technical skillset and his "radical" pedigree, he was a pretty easy suspect for Rawshark.
This was common knowledge among the political class and he has been approached by senior journalists who thought he was Rawshark. When the Prime Minister says he knows who Rawshark is, he is probably talking about Rangi.
Ben has claimed in the past that he sympathises with Rangi and was protecting him. Throughout Ben's engagement with Slater, he dropped "inside information" about Rangi - that he's been interviewed by Police, that he's been arrested, that he's been summoned to court. None of that was true.
At the same time, he was also receiving payments from Slater to work on a book to out those who conspired against him, and as a part of this, he attempted to solicit a confession out of Rangi. This is often explicitly referred to as "social engineering", and once, as a fearless "mind battle".
21 Jan 15 08:30:37 - BR: Hi Cam. Ready to send off the stuff shortly and I've also got some ideas on how to push back. 0304*********** for compo and then we are good to go. I got the perfect way to bait Rangi. Unfortunately I know exactly how his crim mind works. Let's get some smashing done this week. Just let me know! Have a great morning.
23 Jan 15 15:23:04 - BR: So, I got Rangi to admit he's RS, got proof from him ie the encryption key, and I've been fearlessly waging a mind battle with them.
28 Jan 15 14:29:14 - BR: I'll provide this and more writing upon ____ lol. I'm honey potting Rangi too.
30 Jan 15 12:10:48 - BR: I'm entrapping Rangi to break suppression on something
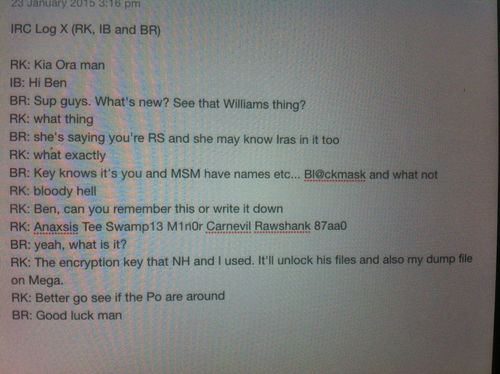
And what exactly is this "proof... ie the encryption key"? Ladies and gentlemen, here is the smoking gun, the evidence Ben provided to Slater (verbatim):
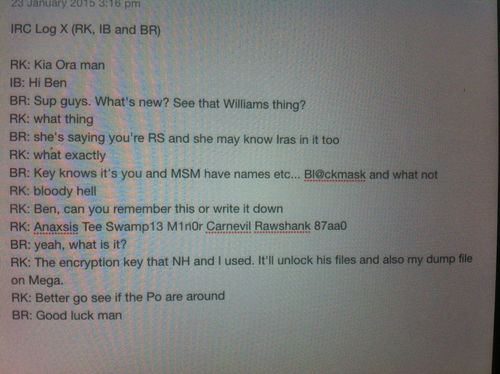
If it's not clear to you already, this is no smoking gun. This is a ludicrous and obvious hoax. Rangi is no stranger to interacting with the Police, and Rawshark has shown a clear aptitude for not being caught. Yet this conversation - which supposes Rangi is Rawshark - shows him throwing up his hands the second Ben says that the game is up, and accepting his imminent arrest with a simple: "bloody hell". And that the first and only action he takes on hearing this news is to hand over the key to his incriminating evidence to first person he sees, as opposed to the more rational course of action of, ya know, *not* handing over the key to his incriminating evidence to the first person he sees.
This is, in short, laughably stupid.
Rangi, for his part, says that that was definitely not him. He confirmed that Ben had been talking to him, but that he was suspicious of Ben right from the beginning. He adds that the person who made up that password, with its substitution of numbers for letters, clearly doesn't understand the point of diceware passwords.
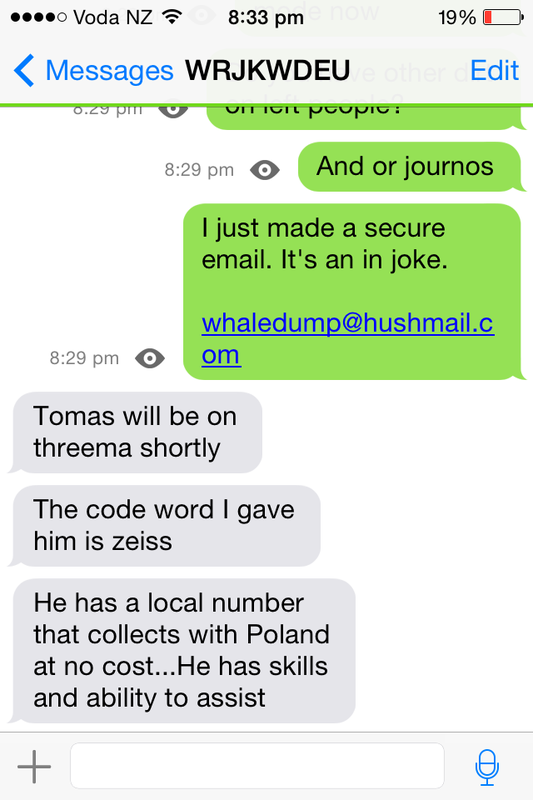
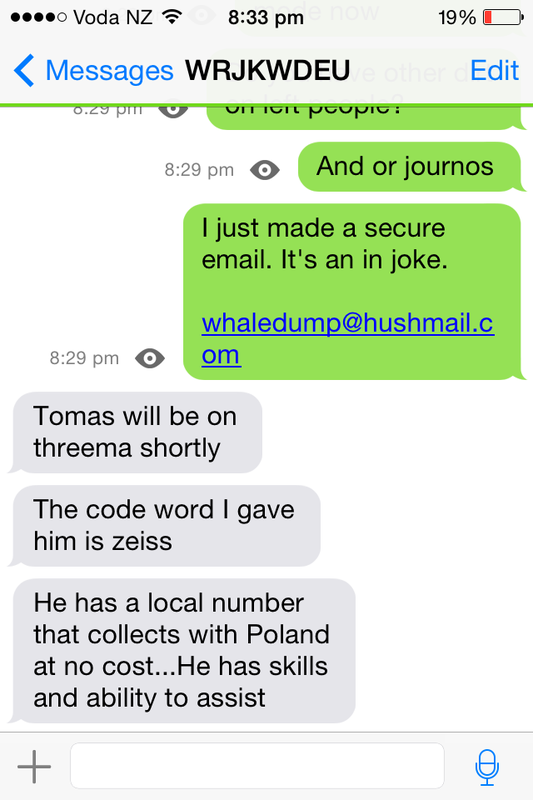
As part of this fearless mind battle, Rangi received an email from "whaledump@hushmail.com", claiming to be Rawshark. Because of Rangi's aforementioned suspicions, he fired off an email to Hager to ask if this was legit. Hager replied that the address is unknown to him, and that it is probably a fake. So Rangi ignored it.
And then the Police raid happened.
Detective Abbot saw the email, printed out on Nicky's desk. Jackpot!
From: RANGI KEMARA!
To: Nicky Hager!
Something something whaledump@hushmail.com!
[Disclaimer: Not actual content/header of email.]
Presumably, the Police were already treating Rangi as a suspect at this point.
"We considered [the document] was of interest to the investigation because of information we had already obtained" - Detective Teo
So they find an email from their prime suspect to Hager discussing the criminal conspiracy they're investigating, when in fact, it was just an artifact of the fearless mind battle being waged by Ben:
As for why Rangi was a suspect before this point, or why he was a suspect at all, all I have to go on is this statement by Ben:
09 Feb 15 23:25:18 - BR: Prior to my involvement, no one had a fucking clue about Rangi and Hager.
In the logs, Slater doesn't dispute this. But beyond that, I have no idea whether it's true.
That email, NH025, is fascinating to me because it's chock full of irony. For someone who wanted the glory of being at the centre of things, Ben actually ended up succeeding. The Police (possibly) connected Rangi with Hager because of Ben, then they actually found evidence connecting Rangi with Hager because of Ben. The stuff that he made up were widely believed by the political class, all the way up to the Prime Minister!
Despite the fact that this piece is about all the shitty things that Ben has done, the lies that he's told, it's also about acknowledging that he really did influence the course of events, and fooled a lot of very powerful people.
But he also did a lot of pretty shitty things.
--
Blackphone/Black Ops
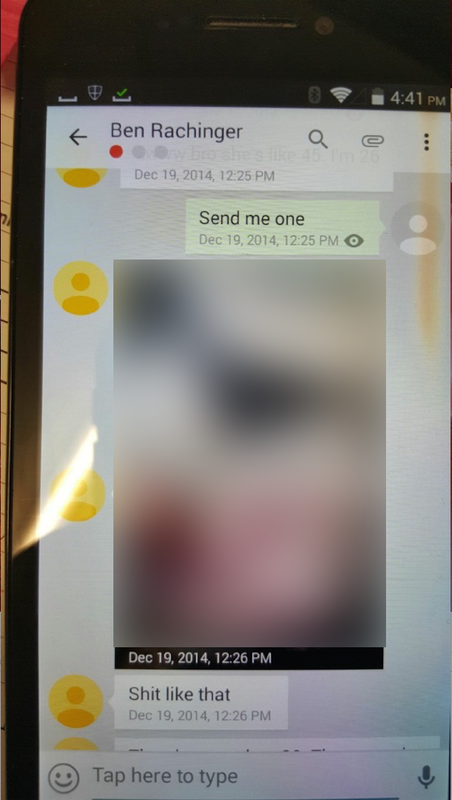
In June this year, after Ben's story on The Nation (accusing Slater of commissioning Ben to hack The Standard) came out, a blog released private photos of a senior political journalist. It had the very clear purpose of distracting attention from Slater and discrediting Ben.
I now have definitive proof of how those photos got into the hands of that blog.
This was the log of the Threema chats between Ben and Slater on 19 Dec:
19 Dec 14 12:23:44 - BR: I play a game online but I'm always straight w you here
19 Dec 14 12:24:11 - BR: I blame the Govt for throwing people like us to the sheep that want to be wolves
19 Dec 14 12:24:21 - BR: I hope John hasn't actually abandoned you
19 Dec 14 12:24:25 - BR: Oh
19 Dec 14 12:24:50 - CS: Yes...john key lost my respect
19 Dec 14 12:26:43 - BR: Shit like that
19 Dec 14 12:42:42 - CS: How unethical
19 Dec 14 12:43:18 - CS: If only she knew
19 Dec 14 12:43:21 - BR: Pray tell?!
19 Dec 14 12:43:28 - BR: Lips sealed
19 Dec 14 12:43:41 - CS: When we meet
19 Dec 14 12:44:10 - BR: I'll make a new folder
19 Dec 14 12:46:02 - CS: I'm sick of these unethical journos attacking me
Note the non sequitur and missing time after 12:24. Here is one of the photos which was posted on that blog (original photo on the blog was unblurred):
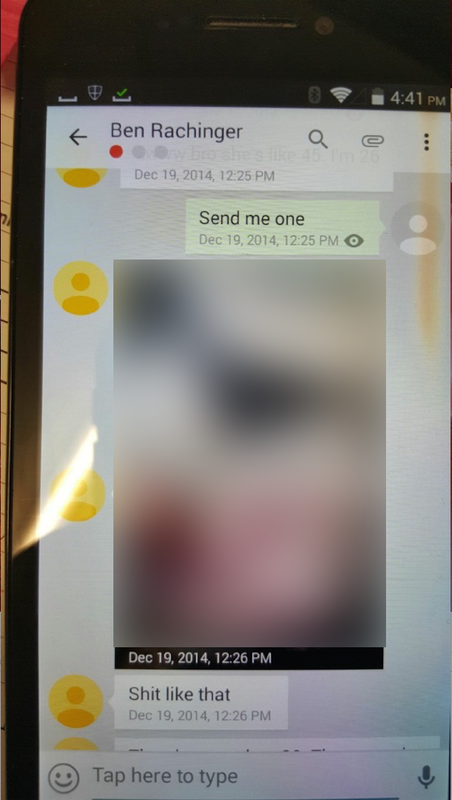
Note the timestamp on the photos and the line "Shit like that": 12:26 on 19 December. The photo is clearly showing the Threema conversation between Ben and Slater. Note that Threema shows the name of the person you're talking to, not your name. This is showing Slater's side of the conversation, not Ben's.
Just for a final nail in the coffin, note the icon on the top left of the screen. That is a "space switcher" icon used by SilentOS, the operating system for Blackphones.
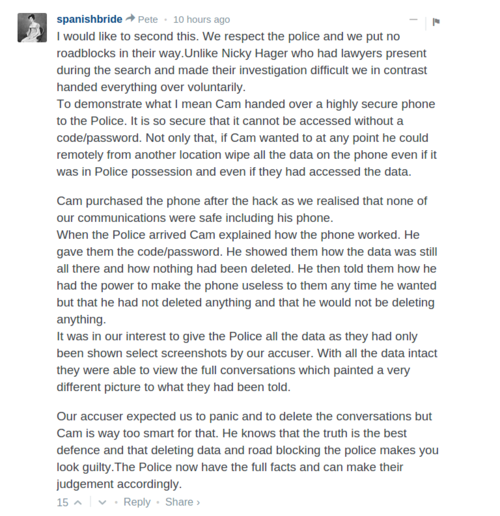
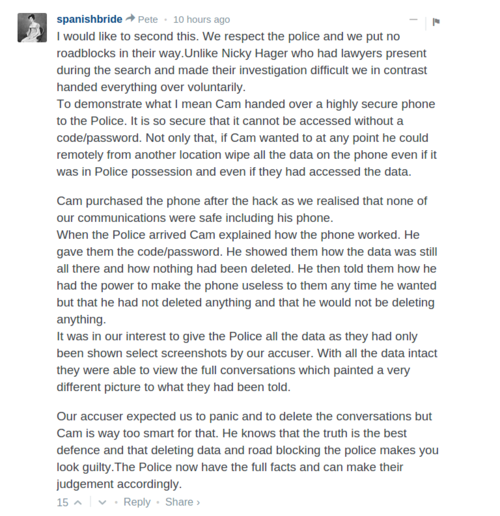
Last weekend, Slater's wife said that Cameron used a specialised "highly secure phone" which could be remoted wiped:
In the Threema logs, Slater says:
06 Jan- 15 17:43:44 - CS: I have a black phone...no cops have been near it
The upshot is that the photos which appeared on that blog are photos of Slater's Blackphone, showing the conversation where Ben sent those photos to Slater. Ben's previous claims that those photos were hacked from his phone is a lie. He sent them. And unless Slater wants to claim that his "highly secure" and remotely wipable phone was stolen, unlocked, photographed then put back, it's also clear that Slater actively participated in that release.
(Note that I received the Threema logs in May, though I wasn't able to unlock them till July. The blog post containing the private photos came out in June. It is not possible for the Threema logs to have been doctored in response to the blog post.)
--
Can HAZ weekly pay? Lol
From late November 2014 to end of January 2015, Ben strung Cameron Slater along for money. Every couple of days, he would ask Slater for cash. The early payments were not for "hacking The Standard". They were payment for helping Slater, Cathy Odgers and others write a book exposing the plot against Slater. Ben's role was in detailing how the conspirators of this plot (including Rawshark) were tracked down, and in providing background on the hacking underworld.
25 Nov 14 10:53:09 - CS: I want you to sit with Cathy and tell her your story for the book
25 Nov 14 10:53:16 - CS: I'll pay you for it
25 Nov 14 11:00:00 - BR: Haha want to advance me 50-100 dollars? I've already written up so much. Would appreciate a helping hand today.
25 Nov 14 11:02:33 - CS: How about $500
25 Nov 14 11:02:52 - CS: Send me your bank account
25 Nov 14 11:04:49 - BR: Westpac or ASB? What's best for you. Ps you're the fucking man
25 Nov 14 11:09:11 - CS: Westpac
25 Nov 14 11:09:32 - BR: Man, this is huge. I never doubted you and have always maintained my silence.
25 Nov 14 11:09:43 - BR: Doing this for me is humbling
25 Nov 14 11:09:54 - BR: I can't tell you how much it means
25 Nov 14 11:12:33 - CS: Check your bank
25 Nov 14 11:14:53 - BR: Maaaaaaaate.
25 Nov 14 11:15:07 - BR: Mate. You're a very good person.
25 Nov 14 11:17:58 - CS: Right let's start lining up these pricks to take them down
25 Nov 14 11:37:34 - CS: In hagers book he links Cathy to Russians and Chinese so we will hide you by calling you an offshore specialist
27 Nov 14 18:00:33 - BR: Ok so I've collated all the screenshots, records of chat logs, meeting minutes w cops and a list of the evidence they have. Also I've collated a short report on the whole journey from book release until now. It's a bit lengthy but I want to put it in a google drive and send you the link.
That's a really valuable set of evidence. Thanks for your assist the other day.
Like to reach out to you for more money. Doesn't have to be a lot but we have almost nailed these pricks and I can do w maximum financial assistance. I won't require any further payment for the book etc and happy to have done what I've done so far :-)
Really appreciated if you're in it to win it, Cam. Seeing cactus tomorrow morning. Compiled report today.
Throughout this period, Ben kept Slater on the hook with purported inside information from his role as an "undercover agent" for the Police. The common theme was that action was imminent.
According to Ben, Slater's many enemies were all being targeted by Police, many had been questioned, and arrests were imminent, or had already happened. In order for the momentum to continue and for the "last stage of our triumph" to be achieved, more money was required.
30 Nov 14 17:24:16 - BR: Yo, just left a short meeting with cops. They are planning to move within days.
30 Nov 14 17:24:25 - BR: Definitely this week.
30 Nov 14 17:25:05 - BR: Coming, that is. They want to set up a bit of a tricky meeting where the perp and I meet in public and then they move on him.
30 Nov 14 17:25:24 - BR: Simultaneously they will be arresting three other people.
30 Nov 14 17:25:46 - BR: They have insufficient on KDC at this stage to arrest him in this case.
30 Nov 14 17:27:34 - BR: I don't know how I feel about being there for arrest
30 Nov 14 17:37:53 - BR: But that's all pretty exciting!
30 Nov 14 17:42:55 - CS: Woe...do you know who other three are
30 Nov 14 17:51:27 - BR: I'll try to find out. Got another meeting in a hour w some senior cops :-|
30 Nov 14 17:52:25 - BR: They advised me to say nothing whatsoever to anyone, FYI.
30 Nov 14 17:53:12 - BR: Ok so I've got the meeting tonight and another meeting tomorrow. Pretty crucial you have some sort of write up prepped in advance for the blog!!
30 Nov 14 18:04:41 - BR: Ok so on a serious note. I know you are getting paranoid but you need to chill. I'm working hard and need to get the next two days done and then our worries are over!! Special request. Have to buy some USB drives and also a lot of caffeine and tobacco so this plan goes straight. I don't need another 500. 180 will get me everything I need today. Please trust me and assist this last stage of our triumph.
This was mixed in with some straight-up flattery...
03 Dec 14 15:41:36 - BR: Hey man, last request. They're actually going to have my electronics for at least a month. Need a $500 loan to get another laptop. It would be much appreciated because there's still so much I can do for Team Cam. I'm accom sorted etc. Let's kick ass and send names to a police hotlist. I've made the contacts, you have so much to teach me.... I know I can learn so much from you. You're like Severus Snape from Harry Potter books IMO. Hope you can help me out
...veiled threats...
10 Dec 14 12:34:44 - BR: Cam, I really need one last bit of help. Up to you but I'm going through hell for you and I'm keeping all the secrets. I'll be destroyed publicly and with Anon if they find out about any of us. The money keeps me floating and fighting. Up to you.
...and special deals.
19 Dec 14 13:06:49 - BR: I'll send you pics and screenshots. I do have dirt on a Fisher. One thing, can you loan me some $? I'll send pics and stuff for sure. I'm on bones of my ass. Let's fuck these unethical journos up.
Slater wanted to believe his Great Day of Reckoning was arriving, and Ben was happy to help. He wanted to believe, even after these "imminent" arrests were delayed time after time, even when the information he was given was laughably bad, even when he had himself discovered the information was false.
05 Dec 14 15:41:46 - BR: He's been served
05 Dec 14 15:42:10 - BR: Summons
05 Dec 14 15:42:18 - BR: Told you I'd come through man
05 Dec 14 15:42:30 - BR: You must have doubted me
05 Dec 14 15:42:35 - CS: Summons to appear in court?
05 Dec 14 15:43:18 - CS: Mate when you have been under attack.like I have it is v. hard to trust
05 Dec 14 15:44:05 - BR: I can only imagine
05 Dec 14 15:45:51 - BR: Last last request (lol), I have to keep floating and alert for next week or so. Financial help appreciated. We got them.
05 Dec 14 15:46:15 - CS: Now we need the info for the book
05 Dec 14 16:37:23 - CS: He's still tweeting...why isn't he in the clink?
05 Dec 14 16:49:17 - BR: Court summons is diff to clink
05 Dec 14 16:49:26 - BR: Cos he's on parole ish
05 Dec 14 16:49:36 - BR: They want to deal with it this way
05 Dec 14 16:50:58 - BR: But he's been charged
05 Dec 14 16:51:06 - BR: He's sending me angry messages
05 Dec 14 16:51:15 - BR: Will have to go off grid :-//
05 Dec 14 16:52:28 - BR: Now comes the danger time for me
05 Dec 14 16:54:06 - BR: Let's see if I get through it
05 Dec 14 16:58:05 - BR: I leave the finances in your hand, Chief. Going OL for a few hours at cops reco.
This happened so regularly that it actually became a running gag:
28 Jan 15 08:55:57 - BR: Sweet. Done a big report for you w a lot of docs.
Can HAZ weekly pay? Lol
Slater's willingness to believe was almost boundless. Almost. When the deal to hack The Standard was struck, the price was set at $5000, with $1000 upfront. But on the day of the delivery:
07 Feb 15 08:13:30 - BR: Inform the client you have the file and it's encrypted. I'm still very much worried. 1k is good but so is being free and non charged, or non blackmailed. Half remainder upfront and you get key within hours. Or you can try crack the encryption! Client will understand if I'm hacking on their behalf. Cheers. Got to run as moving place again this morning. Too many missed calls and a herald journo scoping me out at this location.
07 Feb 15 08:23:35 - CS: Mate that wasn't the deal...I've exceeded the deal...you asked for 500 down payment...you've had 1000...I've also helped you financially for months...I've never let you down
For the first time in three months, Slater didn't pay. So later that day, Ben gave Slater the decryption key anyway, "on trust" that Slater will pay. One catch though:
07 Feb 15 17:23:39 - BR: The links inside are to the doc dumps and diagrams. Trusting you. You just have to guess the encryption method ;-)
Not surprisingly, "guess the encryption method" was a wild goose chase. And finally, after three months of this bullshit, Slater has finally had enough, and this long protracted con came to a definitive... late middle.
09 Feb 15 22:57:51 - CS: I did that help you out...but you've got to want to help yourself...its very frustrating...if I replayed all the things you've promised me and lined them up beside what has been delivered...well its lots vs nothing...and I'm about done with it all
09 Feb 15 23:04:22 - BR: A lot versus nothing?
09 Feb 15 23:04:31 - BR: That's an interesting perspective.
09 Feb 15 23:16:19 - CS: Tell me what I've got...other than a nearly $5k hole in my account...you said you'd help with the book...nothing...we had a deal and what I've got is an email of gobbledegook...my rep is on line with funder...I can't show them a single thing...I think you are taking the piss with me now...
09 Feb 15 23:17:49 - CS: I've been completely straight all the way...tell me I'm wrong...coz right now I feel like a trusting fool
09 Feb 15 23:19:21 - CS: I've fought these fucks as they've laughed at me...pried through my private life...and so I believe someone when they come to help...I try to help them because I'm like that...and as usual I'm the one burned
At this point, even I feel sorry for Slater. Ben was very obviously taking the piss with him, and still, Slater is so isolated and desperate that - even after saying out loud that this is just all just a scam - he still can't accept that this was all just a scam. Ben feigns outrage and indignation, declares that he's "on Team Cam, dw" the following day, and things return to normal.
11 Feb 15 22:16:02 - CS: I've talked to funder...bonus is avail for info on Nippert etc
11 Feb 15 22:16:28 - CS: Just reviewing twitter from back then...I bet juha was involved too
12 Feb 15 00:41:15 - BR: Definitely
12 Feb 15 00:41:21 - BR: He's been very cagey
12 Feb 15 00:41:40 - BR: I'll have the info to you tomorrow re Nippert and Ng, no problem.
12 Feb 15 08:08:49 - CS: OK cool
12 Feb 15 08:30:46 - BR: Yeah so it's the IP addresses of the two phones Ng and Nippert used for WD. They used disposable hushmail email for login. They also transmitted some documents but never been able to find those because phones got smashed after WD2 went down.
Conclusive Proof of WD = Ng and Nippert
1. IP leakage
2. Semantic analysis of the two blended has a 92% probability of a match.
3. In emails, Ng alludes to having inside knowledge of hack and RS.
4. Ng is, ofc, very close to Kim. Who's a prick.
Low on net. When I get going today, will dump the Ng and Nippert files on you.
The morning after Slater offers a bonus for dirt on "Nippert etc.", Ben wakes up with definitive proof that Nippert and I are Whaledump. For what it's worth, "blended semantic analysis" makes as much sense as a facial recognition match based on one of those "what would your baby look like" photos. And, as should be obvious by now, the evidence never arrives. Two days and another $500 later:
14 Feb 15 08:32:25 - CS: Nice one mate...you got me again...shit I'm a dumb trusting cunt
14 Feb 15 09:43:38 - BR: I sent it!!!! I'll go and resend now but I sent it before bed
14 Feb 15 14:19:41 - BR: Got it yet?
14 Feb 15 14:19:47 - BR: I sent it in triplicate
14 Feb 15 14:37:27 - CS: I'll go look again
And he did. This goes on for another two days. Until Ben declares war on Slater by posting their messages online.
16 Feb 15 16:57:26 - BR: Time to dance
16 Feb 15 17:00:50 - BR: I'm not releasing anything derogatory or bad about you
16 Feb 15 17:00:53 - BR: My promise
16 Feb 15 17:00:59 - BR: But I'm done
16 Feb 15 17:06:55 - BR: I'm broke alone and going crazy. Sorry man. Too much for me.
--
I tried to talk to Ben face-to-face for this article. Last time I flew up to Auckland to meet him, he was suddenly unreachable. And I'd arranged to meet him again this week, but he cancelled again, flipping between claims that he's keen to talk but just can't make it, an aggrieved "let's battle shall we?", that Police action on the Slater case is imminent, that he (Ben) might be arrested soon.
Obviously, having seen how he played Slater, I wasn't buying it. But I went along with this for months in an attempt to get another face-to-face conversation with him, because I thought - I believed - that when confronted with the black-and-white evidence, he would tell me the truth. A definitive, unifying truth which would make sense of this whole fucking mess.
Oh man, I wanted to believe.
--
Postscript: So, *is* Rangi Rawshark? I asked, and here is his "clear as mud" response.
Am I Rawshark? I think it is clear from what transpired over the last year that we all are in a sense, anyone that takes direct action in the way that Rawshark did to blow the lid off empathyless activities of the powerful. All I ask is that one day I can have a beer with the real Rawshark, and shake her hand, that would indeed be an honour. Chur!
--
If you enjoyed/had an aneurysm reading this post, please consider putting some money in my tip-jar.