Until this week, relatively little published from Edward Snowden's trove of NSA documents has concerned New Zealand and its specific role as a "Five Eyes" intelligence partner. Kim Dotcom's lawyers have revealed to us more of our own security business than Snowden has.
But yesterday, Snowden's journalistic ally Glenn Greenwald released another tranche of documents, alongside his new book on the Snowden story, No Place to Hide. And finally, we're in the picture. David Fisher summarised some of the key points (from yet another Powerpoint presentation, in this case for a Five Eyes conference in 2011) thus:
* our GCSB spies were shown instructional slides on how to operate the X-Keyscore surveillance program which trawls mass harvested email addresses, phone numbers, online chat, web-based email and attachments sent;
* they were privy to diplomatic espionage by other Five Eyes partners, including spying which was Canadian spies capturing the emails, text messages and phone calls between the Brazilian president and her aides;
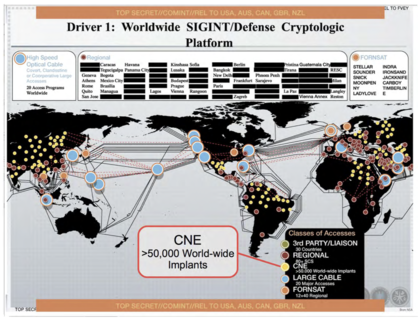
* they were briefed on the NSA's efforts to deliberately put backdoors into private companies' computer networks;
* and the were given access to a program called "Homing Pigeon" which allowed in-air communications on passenger jets to be monitored.
One NSA document tells New Zealand and its other "Five Eyes" intelligence partners the ambition is to "know it all", "collect it all", "exploit it all" and "partner it all".
It's going to take a while to read, let alone analyse the significance of the new documents, but this slide on Five Eyes' "New Collection Posture" makes for an interesting start:
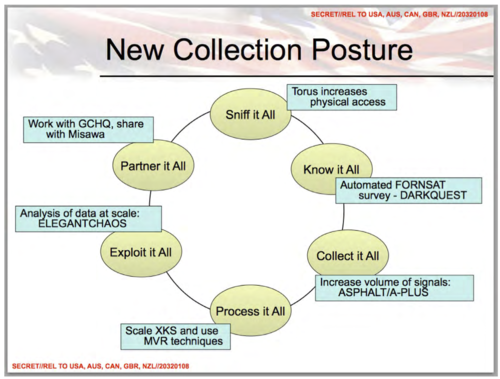
How does "sniff it all" sit with this assurance last week from GCSB director Ian Fletcher?
He also offered an assurance that neither the GCSB or any foreign agency was engaged in the mass collection of metadata or information about New Zealanders' communications which can be sifted for patterns that might point to areas of interest for authorities.
"We don't do that stuff. It's important to keep on saying that."
He also offered an assurance that neither the GCSB or any foreign agency was engaged in the mass collection of metadata or information about New Zealanders' communications which can be sifted for patterns that might point to areas of interest for authorities.
And how exactly does "partner it all" describe the relationship between the GCSB and foreign intelligence agencies and what information is deemed appropriate to share? How does "share it all" tally with John Key's assurance that the GCSB does only "limited sharing" with the other agencies?
The problem here, as it was with the very first Snowden story, is that we're trying to derive meaning from a Powerpoint slide full of slogans and jargon. We're not going to get the answers by just looking at slides.
By coincidence, this week the GCSB and the National Cyber Security Centre (NCSC) released their "guidance" for New Zealand network operators, which sets out the expectations under the Telecommunications (Interception Capability and Security) Act, which passed last year. Among other things, the agencies will effectively have a say over network design:
Network operators must notify GCSB when changes to their networks are proposed and GCSB may need to be involved ahead of any network infrastructure purchases.
One obvious motivation for such a requirement would be to avoid the danger of compromised infrastructure. But if GCSB has been briefed on NSA's own efforts to compromise commercial network products, has it -- or would it -- waved through software or hardware it knows to contain such a backdoor?
Efforts by Britain's GCHQ to develop malware to compromise personal computers (and, among other things, turn on their cameras and microphones) were the subject this week of a legal challenge from Privacy International. And American legislators are this week pushing back against language in the bizarrely-named USA Freedom Act that seems to allow the NSA to exploit vulnerabilities it finds in software, without revealing them to vendors or the public.
There's an obvious hook in the documents for Australians. Their security agency explicitly asked the NSA to spy on Australians of interest. Few Australians are going to object to the surveillance of known or even suspected terrorists. They would be justified in wanting to know some more about where the boundaries lie.
Wired has an interesting precis of Greenwald's account of the fairly messy way the Snowden documents first made their way to the headlines. Greenwald himself hasn't come off entirely well in other published narratives so it's useful to have his version in detail.
This is clearly going to take a while to unwind. But these things seem important for us to talk about.
The documents released yesterday are here, bundled into a 12.9MB PDF.